SAP GRC Training Online | SAP GRC Course with Real-Time Projects
Trusted by 20,000+ professionals across India, the US, and Middle East.
SAP GRC Training
At UnoGeeks, our SAP GRC Training and Course Online is designed to make you project-ready and placement-focused from day one. With organizations increasingly focusing on security, compliance, and risk management in SAP S/4HANA environments, the demand for skilled SAP GRC consultants is growing rapidly across global enterprises. Professionals with expertise in Access Control, Process Control, Risk Management, user access governance, compliance monitoring, and audit management are highly sought after in today’s job market.
SAP GRC professionals today command strong salary packages, with freshers securing competitive entry-level roles and experienced consultants earning high-paying positions in top consulting firms and MNCs. Our training goes beyond theory with real-time GRC implementation scenarios, hands-on system configuration, live project exposure, and interview preparation to make you fully job-ready.
By the end of the program, you won’t just learn SAP GRC concepts — you’ll be ready to crack interviews and step into real SAP GRC consultant roles with confidence.
Our Students Work At
For Quick Questions
SAP GRC Training Videos
Get Course Full Syllabus
SAP GRC Training Course Details
About SAP S/4HANA GRC & Security
SAP S/4HANA GRC (Governance, Risk & Compliance) and Security is a critical solution that helps organizations manage user access, compliance, risk management, and audit controls across SAP systems. It ensures secure and compliant business operations by controlling access to sensitive data and preventing fraud or unauthorized activities.
It enables organizations to enforce security policies, automate risk analysis, ensure regulatory compliance, manage user provisioning, and strengthen audit readiness using SAP’s advanced GRC framework integrated with S/4HANA environments.
Key Features & Capabilities
• Access Control Management – User access governance, role design, and Segregation of Duties (SoD)
• Risk Analysis & Remediation (RAR) – Identify, analyze, and mitigate security risks in real time
• User Provisioning & Role Management – Automated access request and approval workflows
• Super User Privilege Management (SPM) – Monitor and control elevated access usage
• Process Control & Compliance – Ensure audit compliance and internal control monitoring
• Security Configuration – Authorization objects, profiles, and parameter setup
• SAP System Security – User administration, role creation, and troubleshooting
• Audit & Reporting – Compliance reporting, risk dashboards, and monitoring tools
Become a Certified SAP GRC Consultant
Looking to build a high-paying career in SAP GRC & Security?
Join UnoGeeks’ Best SAP GRC Training Online Program — trusted by professionals and recognized as one of the top SAP GRC training institutes in the market.
We focus on real-time GRC implementations, certification guidance, and job-oriented skills — not just theory.
What You Will Learn
• Introduction to ERP, SAP & R/3 architecture and navigation
• SAP user administration and security role concepts
• Master security tables, transaction codes, and troubleshooting
• Authorization concepts and profile parameter configuration
• SAP GRC overview, project lifecycle, and implementation approach
• Risk Analysis and Remediation (RAR) configuration in detail
• Super User Privilege Management (SPM) and access control
• Enterprise role management and user provisioning workflows
• Hands-on SAP GRC Live Project implementation
• SAP GRC certification guidance and exam preparation
• Resume building + mock interviews with personalized feedback
• Job readiness support with regular SAP GRC job openings and referrals
🔔 Daily SAP Job Alerts by UnoGeeks
Follow us on LinkedIn for real hiring updates:
👉 UnoGeeks SAP Jobs & Placement Updates
Who Can Enrol in This Course?
• IT professionals looking to build a career in SAP GRC & Security
• Graduates & post-graduates aiming to start their career in SAP S/4HANA GRC
• Freshers seeking high-paying IT roles in SAP security and compliance
Prerequisites
No prior SAP or security experience required.
We cover all foundational concepts as part of the training:
• Basics of SAP and ERP systems
• Introduction to security and compliance concepts
• Business process understanding in SAP environments
Register for a Free Demo
SAP GRC Course Curriculum
- Introduction to ERP
- Introduction to SAP & R/3 Architecture ASAP Methodology
- Introduction to HANA AND 54 HANA
- Modules in SAP and their coverage
- Overview of ABAP, BASIS, MM, PP AND SD
- Global Settings
- Login
- Sessions
- SAP Screens
- Features of SAP Navigations
- Features of SAP Easy Access Screens
- Features of Implementation Guide Screen
- User Administration (SU01)
- User Creation
- User Modification
- User Deletion
- User lock/unlock
- Password Resetting
- Mass User Administration (SU10)
- User Groups
1.Tables Related to User Administration
2.Explain USR40 table.
3.SAP R/3Authorization Concept
- Role administration using PFCG.
- Single roles
- Composite roles
- Derived roles
- Role Transport from Dev to QA & QA to PRD
- Authorization objects
- Authorization in Role administration
- User Buffer/Roles
- Missing Authorization (SU53, 5T01)
- Tables Related to Roles (AGR* Tables)
- Maintenance of Authorization objects (SU24)
- Difference b/w SU24 & SU22
- Troubleshooting (SU53, SU56andSTO01)
- Protect Tables and Transaction codes and Programs.
- User Information System (SUIM)
- Security Audit System (SM19, SM20)
- Custom authorization objects
- Password Profile Parameters
- System Profile Parameters
- Central User Administration (CUA) (SM59, SCUA, SCUM, SCUG)
- GRC Applications, Requirements, and Benefits
- GRC Landscape
- GRC Release Roadmap and Compatibility
- Understand project planning.
- Understand key stakeholders in project.
- Project Implementation Considerations.
- Understanding RAR functionality
- Pre- and post- installation check lists
- Understanding segregation of duties (SOD)
- Understanding RAR data requirements
- Conducting risks and rules workshop
- RAR rule building exercise
- Understanding Remediation and mitigation strategy
- Configuring RAR
- Troubleshooting RAR
- Understanding SPM functionality
- Pre- and post- installation check lists
- Understanding SPM data requirements
- Understanding Fire Fighter strategy
- Understanding SAP role, Fire fighter ID and end user ID mapping
- Configuring SPM
- Troubleshooting SPM
- User provisioning process workflow: Role request
- Advanced workflows
- Master data and process logic
- Reporting
- Workflow engine
- Compliance exercise and summary
- Pre- and post- installation check lists
- Conclusion
- Implementation Methodology in ERM
- Role Generation using ERM
- Pre- and post- installation check lists
- Integration with CUP and RAR
- Proposals in PFCG and GRC
- Implement SAP GRC & SECURITY for a Live Project.
- Understand the requirement and come up with config workbooks.
- Configure SAP GRC & SECURITY as per config workbook.
- Implement SAP GRC & SECURITY Modules as per Config Workbooks
- Test the setups.
- Explain various SAP GRC & SECURITY Certification Options
- Discuss Important SAP Certification Exam Questions
- Prepare for SAP GRC & SECURITY Certification
- Prepare Crisp Resume as SAP GRC & SECURITY Specialist
- Discuss common interview questions in SAP GRC & SECURIT
- Provide Job Assistance
🎥 Watch How We Teach SAP GRC
🎓 Learn From Our Most-Watched real-time SAP GRC Sessions
For Quick Questions
SAP GRC Training Videos
Get Course Full Syllabus
SAP GRC Lead Trainer – Industry Expert for SAP GRC Training at UnoGeeks

100+ Live Batches Delivered
2000+ Professionals Trained
20+ Years SAP GRC Experience
Mr. Rohit is the Lead SAP GRC & Security Trainer at UnoGeeks and a seasoned industry expert with over 20+ years of experience delivering complex SAP GRC and Security implementations for top US-based product companies and global consulting firms.
He specialises in end-to-end SAP GRC training, guiding professionals through real-world implementations of Access Control, Risk Analysis & Remediation (RAR), Process Control, Super User Privilege Management (SPM), user provisioning, role design, and compliance management along with core SAP Security concepts such as user administration, authorization objects, profiles, and role-based access control.
Having worked on large-scale SAP security and compliance transformation programs across multinational organizations, Mr. Rohit brings deep implementation expertise into every session. His hands-on, project-driven approach ensures learners gain practical exposure to real-time GRC scenarios, audit controls, risk mitigation strategies, system security configurations, and compliance frameworks — enabling them to confidently step into SAP GRC consultant roles and excel in real client projects and interviews.
Earn Your SAP GRC Certification with Confidence
Showcase your expertise with an official certificate recognized by employers.

UnoGeeks Sample SAP Certificate
🎓 Official Certification
Earn an official course completion certificate validating your practical SAP GRC expertise
🔗 SAP GRC Certification
You will easily clear SAP GRC Certified Application Associate exam
🌍 Industry Recognition
Strengthen your resume with widely recognized credential trusted by employers and consulting firms.
🚀 Career Advancement
Gain hands-on SAP GRC Skills that help you stand out & advance in your career
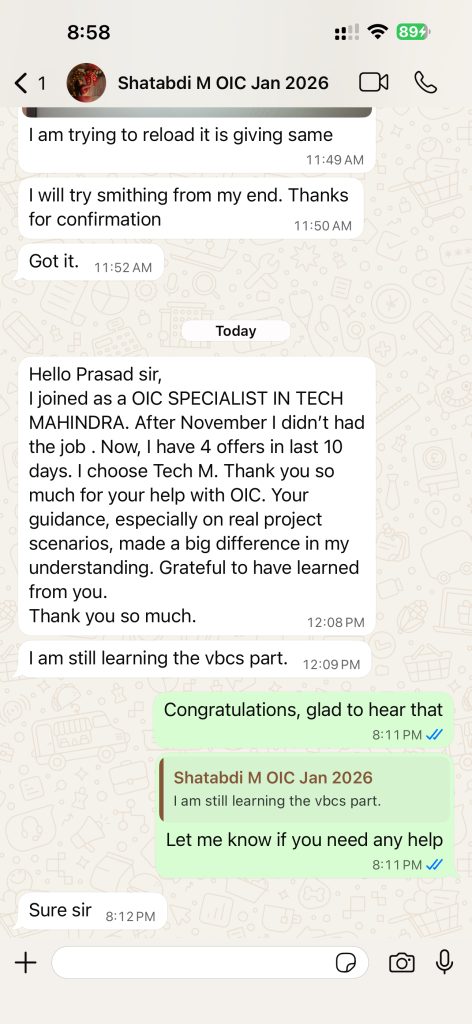
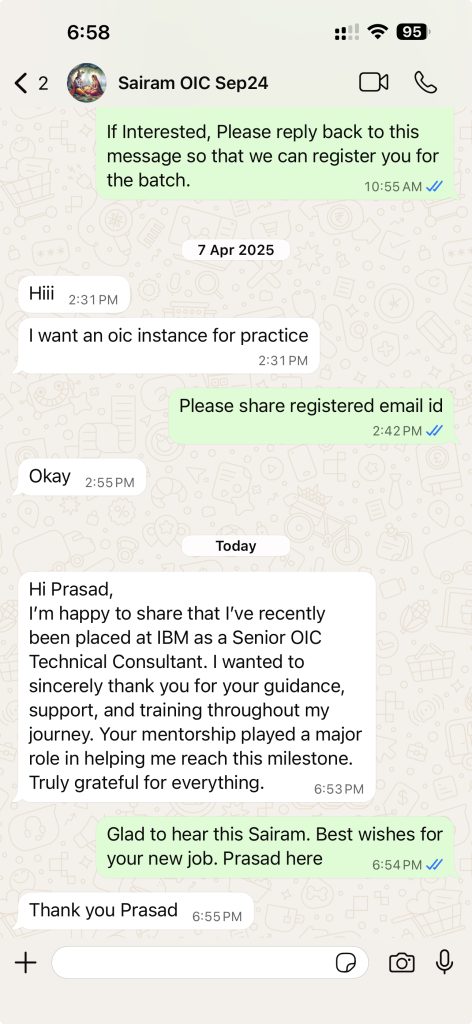
Few Success Stories from Our Students ✅
✅ “Recent real placements & live student messages (updated regularly)”



SAP GRC Consultant Jobs & Salary Trends
📈 High Market Demand
SAP GRC skills are in strong demand as organizations worldwide focus on security, compliance, and risk management in SAP S/4HANA environments. Enterprises across industries require skilled SAP GRC consultants to manage access control, user provisioning, risk analysis, audit compliance, and governance frameworks — creating thousands of job opportunities across consulting firms, shared service centers, and global enterprises.
🏢 Used by Global Firms
Leading organizations across banking, manufacturing, healthcare, retail, IT services, and multinational enterprises rely on SAP GRC solutions to secure and govern their business operations. SAP GRC consultants play a key role in implementing Access Control, Process Control, Risk Management, and compliance monitoring, ensuring segregation of duties (SoD), audit readiness, and secure user access management.
💰 Attractive Salaries
SAP GRC consultants earn highly competitive salaries worldwide, driven by increasing demand for professionals with real-time implementation experience in security and compliance. Freshers can secure high-growth entry-level SAP GRC roles, while experienced consultants consistently command premium compensation packages in top consulting firms, MNCs, and global compliance transformation projects.
Our Training Advantage

Learn from Certified Experts
Get trained by Industry-Certified professionals with deep real-world Oracle Cloud implementation experience

Real-Time Implementation Projects
Learn through real project scenarios that mirror actual client implementations & production use cases.

Interactive Live Training Sessions
Highly interactive live sessions with recordings provided, so you never miss a discussion.

Resume, Interview & Job Assistance
Guidance on resume building, interview preparation, and job support tailored to Oracle Cloud roles

Live Demos Before Enrolment
Attend up to 3 live demo sessions to evaluate the trainer, content quality, and teaching approach

24×7 Learning Support
Prompt support for queries, doubts, and technical issues throughout your learning journey.
What Students Say on Google
⭐ Rated 4.8★ by 600+ Google Reviews
Trusted by hundreds of professionals across Oracle Cloud domains
Free Career Call – Talk to Our Training Experts
Get batch details, syllabus, demo schedule, and fee structure — no obligation
+91 73960 33555
Get Batch Dates, Fees & Demo Details
+91 73960 33555
Mon–Sat | 6 AM – 10 PM IST
info@unogeeks.com
For detailed queries
Live Chat
Chat with our support team now
Trusted by 5,000+ learners | 500+ real-time batches completed
Why Students Trust UnoGeeks
500+
Real-Time Batches Completed
5000+
Happy Students
5 *****
Star Ratings
20+
Expert Trainers
SAP GRC Training 2026 Batch Slots
WeekDay Batch 1
Monday – Friday

07:00 – 08:15 AM (IST)
WeekDay Batch 2
Monday – Friday

08:15 – 9:30 AM (IST)
WeekDay Batch 3
Monday – Friday

07:00 – 08:30 AM (IST)
SAP GRC Training FAQs
SAP GRC training teaches Governance, Risk, and Compliance processes within SAP systems, focusing on access control, risk management, audit compliance, and security governance.
With high search demand for sap grc training, sap grc course, and sap security and grc training, this training prepares professionals to manage enterprise security and compliance frameworks effectively.
A SAP GRC course typically covers Access Control (AC), Process Control (PC), Risk Management (RM), user provisioning, role design, SoD (Segregation of Duties), and compliance monitoring.
Searches like sap grc course content indicate that learners want a structured, module-based learning approach with real-time use cases.
Yes, SAP GRC training online is highly effective when it includes live instructor sessions, hands-on system access, and real-time scenarios.
Keywords like sap grc training online and sap security and grc online training show that professionals prefer flexible learning while gaining practical experience.
SAP GRC certification validates your knowledge of SAP Governance, Risk, and Compliance modules, especially Access Control and Process Control.
High search volume for sap grc certification and grc sap certification shows strong demand among professionals looking to validate their skills.
The SAP GRC certification cost varies depending on the certification type and region, but it is considered a valuable investment for career growth.
Searches for sap grc certification cost indicate that learners are actively evaluating ROI before enrolling in training programs.
SAP GRC Access Control training focuses on managing user roles, access requests, approvals, and segregation of duties (SoD) within SAP systems.
Keywords like sap grc access control training and sap grc access control certification highlight the importance of this module in enterprise security.
SAP GRC Process Control training teaches how to monitor internal controls, automate compliance processes, and ensure audit readiness.
Search demand for sap grc process control training and sap grc pc training shows that this module is critical for compliance-focused roles.
Yes, SAP GRC for beginners is designed for freshers and professionals with no prior experience. Training typically starts with SAP basics and gradually moves into GRC modules.
Keywords like sap grc for beginners and learn sap grc confirm strong beginner-level interest.
SAP GRC 12 training focuses on the latest version of SAP GRC, including updated UI, enhanced access control features, and improved compliance capabilities.
Search terms like sap grc 12 training, sap grc 12 online training, and sap grc 12 certification show growing demand for the latest version skills.
A SAP ABAP full course covers everything from beginner to advanced level, including programming fundamentals, reports, data dictionary, enhancements, forms, debugging, and HANA concepts.
Search demand for sap abap full course shows that learners prefer end-to-end training that makes them job-ready.
SAP security and GRC training combines SAP user security concepts with governance and compliance modules like Access Control and Process Control.
Search demand for sap security and grc training and sap grc security training shows that many learners are targeting combined security + compliance roles.
SAP GRC training and certification programs prepare you for real-time implementation scenarios and official SAP certification exams.
Keywords like sap grc training and certification indicate strong intent for job-ready and certification-focused learning.
SAP GRC training typically takes 6–8 weeks depending on course depth and coverage of modules like Access Control and Process Control.
Learners searching for sap grc course often want clarity on duration before enrolling.
SAP GRC course fees vary depending on training institute, course depth, and certification support.
Searches for sap grc course fees indicate that pricing transparency is an important factor for learners.
Yes, SAP GRC is a high-demand career path, especially in industries requiring strong compliance, audit, and risk management systems.
Keywords like sap grc training, sap grc certification, and sap grc security training reflect consistent market demand.
GRC Process Control helps organizations monitor internal controls, automate compliance, and reduce audit risks.
Search terms like grc process control training and sap grc process control training highlight the importance of this module.
Some platforms offer basic SAP GRC free training, but advanced skills and real-time project exposure usually require paid programs.
Keyword sap grc free training shows that users often explore free options before committing to full training.
You will learn access management, risk analysis, compliance monitoring, audit reporting, and SAP security concepts.
Searches like sap grc course content indicate that learners want clear visibility into skills covered.
SAP GRC training is ideal for SAP consultants, security professionals, auditors, compliance officers, and freshers entering SAP careers.
Keywords like learn sap grc and sap grc for beginners confirm a wide audience base.
SAP GRC training offers strong career growth, high demand, and opportunities in global enterprises focusing on compliance and security.
High-volume keywords such as sap grc training, sap grc course, and sap grc certification clearly show increasing demand in the market.
